see also www.thelastlecture.com
So far, spotlight indexing of Papers’ keywords is not possible (while being planned for a future release according to an email that I received today from one author). In the meantime, here is a workaround.
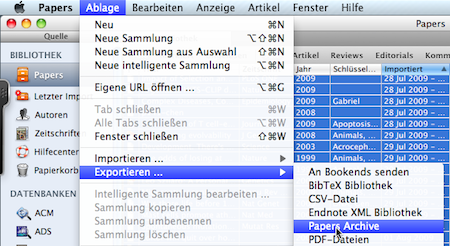
1. Export the whole Papers database as tmp.csv
 Continue reading Spotlight indexing of Papers keywords
Continue reading Spotlight indexing of Papers keywords
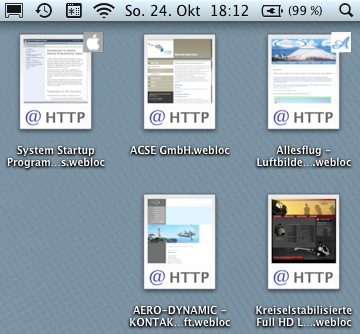
Here comes another mac tip as it is always annoying to move a link on the desktop but loose its associated favicon. Fortunately there is a small program that monitors the desktop (or any other directory) by launchctl and restores the icon. Checkout etWeblocThumb
I tried out everything but only one trick worked. Continue reading R timeout with read.table() and large datafiles
Maybe you discovered also this nifty little arrow that appears in OS X Snow Leopard Mail indicating that a date is being recognized (and can be moved to ical) or an address (ready for transfer into the address book). Continue reading Mail me!
There are certainly a zillion ways how to do create a nice background for your Mac. Here is my favorite method of a weather forecast, an individual calendar and the most recent emails. I created just three geeklets and loaded them in Geektool. Continue reading A living desktop for Snow Leopard
At the Lindau Nobel site we can submit questions to Nobel prize winners. Most of them are trivial or even boring – basically how to make a career or what rank did you have in your university studentship. My proposal to ask there: “Is another information layer on top of the known DNA sequence?” You may want vote for my question, thanks!
One of the best questions so far is “Many people consider the peer-review system broken. If you share that opinion, do you have a solution?” by Clay Barnard.
Roy Glauber, Nobel Laureate in Physics 2005: The current system is pretty poor. So now it’s not a question of spending a lot of money, as it can be resolved very easily without. Good papers last and bad papers don’t. Individuals should rate the papers, although this may not need to be done in an official way.
Sir John Walker, Nobel Laureate in Chemistry, 1997: The peer review system does have problems, but it is the best we have got and I am very much opposed to replacing it with a numerical assessment system. It is a lousy way of assessing people and the pressure to change this system comes from science bureaucrats. This is because it is scientsists making decisions about scientists’ work and the bureaucrats don’t like that; they want to have control.
Jean-Marie Lehn, Nobel Laureate in Chemistry, 1987: That’s an interesting question! I have been interested in it for a very long time. I think we need to have a control otherwise things get in the literature that should not be there …
Filevault is too much of a good thing but slowing down your system and making Time Machine backups difficult if not impossible. No security is also no option, so I thought about creating a sparse image for just a few selected datasets, like mail, calendar, passwords and adressbook. Why should I encrypt 120 Gig when only 8 Gig should be encrypted? The sparsebundle is mounting automatically using a password from the keychain.
I found it, however, difficult to create the correct links that replace the original files.
A Mac OS X hint fortunately explains, how to do that Continue reading Optimized data security under Snow Leopard
(at least for scientists) is the possibility to annotate PDFs. Sorry, the screenshot originates from one the most stupid papers that I read over the past years but it nicely shows Continue reading The most significant improvement in Snow Leopard
A great idea – published now at PLoS ONE today and live at www.biotorrents.net– is a significant step ahead.
The transfer of scientific data has emerged as a significant challenge, as datasets continue to grow in size and demand as open access sharing increases. Current methods for file transfer do not scale well for large files and can cause long transfer times. In this study, we present BioTorrents, a website that allows open access sharing of scientific data and uses the popular BitTorrent peer-to-peer file sharing technology. BioTorrents allows files to be transferred rapidly due to the sharing of bandwidth across multiple institutions and provides more reliable file transfers due to the built-in error checking of the file sharing technology.
Just install a BitTorrent client, read the basics at Wikipedia, and convince your computing department Continue reading Biotorrents
My MacBook Air suddenly died after 3 days of inactivity. The reasons was probably an unattended maintenance job that filled up the 80 GB HD. At least the system became unresponsive while transfering some pictures from a camera to a picture harddisk. And after a hard reset, it let not boot me anymore. This is when the nightmare started…
An already ordered 128 GB SSD did not fit the special requirements of the 1st generation MBA (that need an 1.8” ZIF 4 PATA drive with <5mm height). There seems to be only one product on market by Photofast. Unfortunately a 128 GB HD was not available for the next 4 weeks, while the 256 GB comes at an excessive price tag Continue reading Per aspera ad astra
I find it handy to have a quick link in appointments to the recent correspondence. Unfortunately there is no easy way to do that. Continue reading Mac OSX: Create a symbolic link to Thunderbird Emails in an Ical Appointment
Here is another tech tip to overcome a frequent task – resetting printers and mailers when moving a Macbook around the world: Location X is a perfect solution with a built in autolocate function (depending on airport network! which is superior to IP detection)
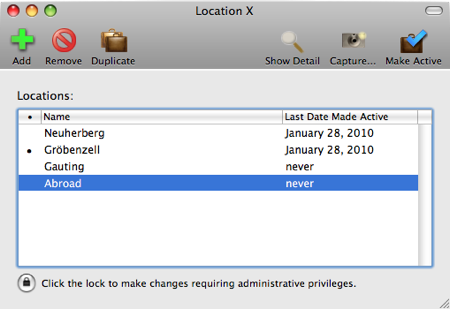
Unfortunately Continue reading Change location
What happens when looking at that video?
The neuroanatomy view this week in Nature
we predict[…] a macroscopic signal visible to functional magnetic resonance imaging (fMRI) in humans. We then looked for this signal as participants explored a virtual reality environment, mimicking the rats’ foraging task: fMRI activation and adaptation showing a speed-modulated six-fold rotational symmetry in running direction. The signal was found in a network of entorhinal/subicular, posterior and medial parietal, lateral temporal and medial prefrontal areas. Continue reading Tear Down the Walls